Samsung has patched a remote code execution vulnerability that was exploited in zero-day attacks targeting its Android devices.
Tracked as CVE-2025–21043, this critical security flaw affects Samsung devices running Android 13 or later and was reported by the security teams of Meta and WhatsApp on August 13.
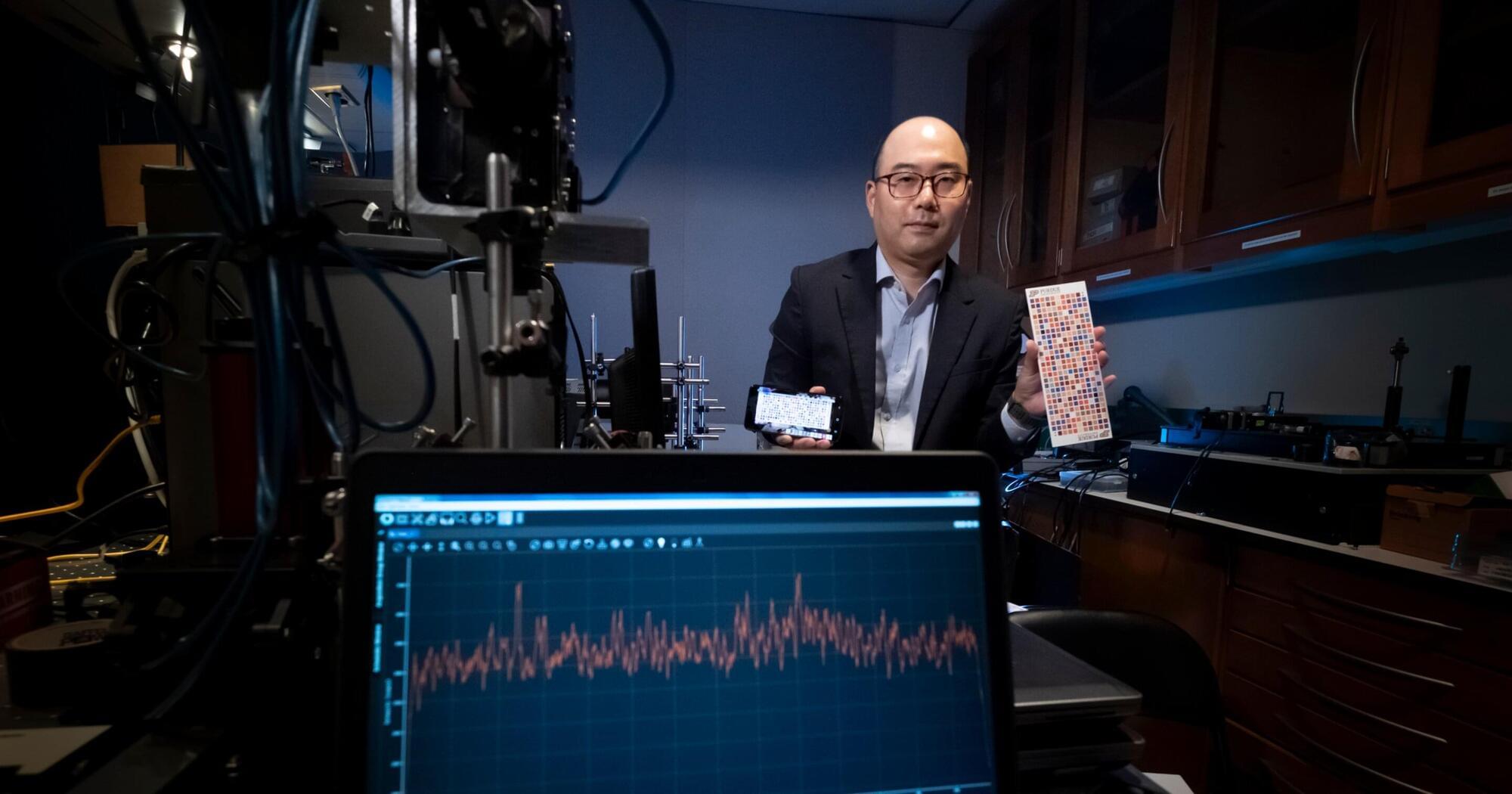
As Samsung explains in a recently updated advisory, this vulnerability was discovered in libimagecodec.quram.so (a closed-source image parsing library developed by Quramsoft that implements support for various image formats) and is caused by an out-of-bounds write weakness that allows attackers to execute malicious code on vulnerable devices remotely.